Challenge description:
Professor M. Eista Hax uses a digital tool to manage all his students. He is very happy with the system, but it does have one drawback: it does not support multiple users. This is a problem, because M. Eista Hax has employees who need access as well. To solve this he writes a super modern, highly encrypted web application to share the password with authorized users. Problem solved.
So… Get that key!
by lama
The page had a login form, and we were able to register an account using a PGP public key. After submitting the public key, the server responded with an encrypted PGP message:
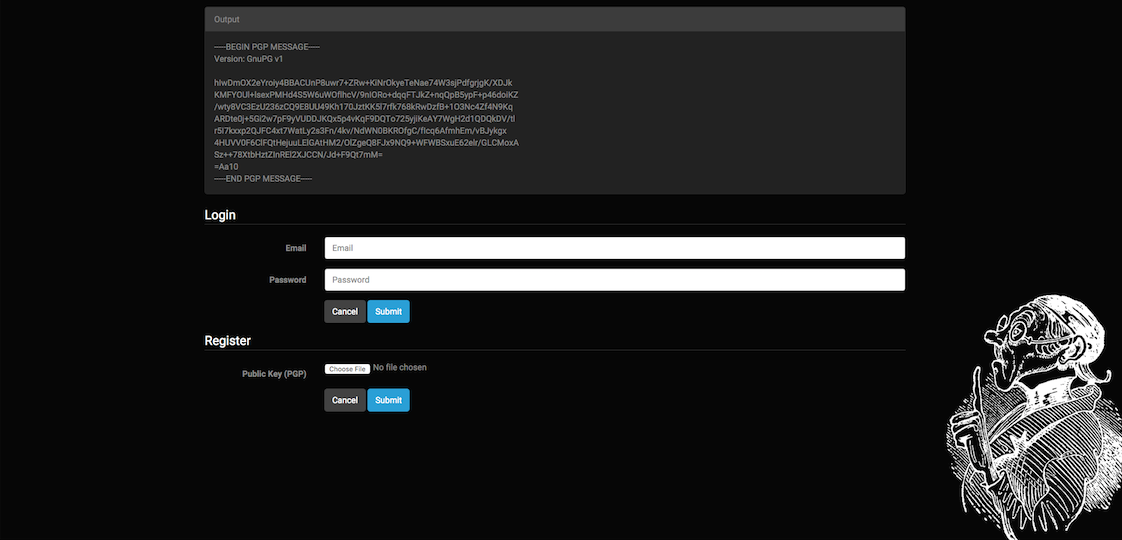
We then used GPG to decrypt the message:
gpg --decrypt-files test.ac && cat test
Hello autoauto@test.de, here is your password: FfLL4ZRtIE6XqpsehDNYYwhh2MGhWD. Your account has to be activated by an admin.%
We registered a user but we were not able to log in, because the account was not activated. We saw that the server was using the email from the PGP public key; maybe there is some database we can attack. Because GPG was checking the email, we first tried to inject into the name field and comment field of the key, but that wasn’t really working. We ended up using https://pgpkeygen.com/, a client-side PGP key generator written in JavaScript. There were basically no restrictions on the email.
You could also patch the PGP keygen.c so the email isn’t validated like so:
| |
This next part took us pretty long, as we had to generate a lot of keys and sometimes the server would not respond. (This was due to the time of the server and our time not matching so that on the server the key was generated in the future. This was fixed later, see Update 1.)
After some time, we got an interesting response using the following email address:
testdsakdsahdsgahdsauzdgsa@test.de' or 1=1 -- f
| |
Our injection worked, but it was filtered since the “=” was removed! So we tried to see which words were blacklisted and if we could bypass it. It turned out that the following words and characters are removed: ( ) % = union select. We also found out that only the first occurrence of a word or character was removed. So it was pretty trivial to bypass the filter.
Next we had to figure out how many columns we had in the SELECT statement using ORDER BY.
union union ' order by 4 -- -
Hello union ’ order by 4 – -, here is your password: RTRmG6EZ6QTbRJ1F9znrYTp6AiEQ2C. Your account has to be activated by an admin.%
()%%()' order by 5 -- f
Hello %()’ order by 5 – f, here is your password: vYzv3I5BQE2nq2wR1meigzCDIXu2x4. Your account has to be activated by an admin.%
sadsadsa' order by 6 -- f
plaintext Account already existing: %
()union select adsada' union select version(),2,3,4,5 -- f
Account already existing: (5.5.44-0ubuntu0.14.04.1) adsada’ union select version(),2,3,4,5 – f [different key]%
OK, nice, that is working. (You can see that the filter is pretty easy to bypass.)
At this point, we were pretty happy we got so far. But we hated the process of generating and decrypting everything manually. Luckily, the first thing we tried next was reading files from the server using load_file before checking the database for more information. It worked! 😀
| |
| |
The first thing that came to mind was: Nice, let’s download the source code of the page. (Later a hint was published as many teams got stuck here.) Triggering a 404 error (curl https://school.fluxfingers.net:1501/asdf) shows that the server is running lighttpd/1.4.33 (Ubuntu 14.04.3 LTS). OK, let’s get the config file:
/etc/lighttpd/lighttpd.conf:
| |
Good, some interesting stuff, but it is PERL 😨.
Anyway, let’s download /var/www/public/index.pl:
This part took us pretty long as we basically had never liked perl. worked with Perl. We saw that we had to log in to get the flag:
| |
We tried to read the config.ini with load_file but no luck. It seemed that we didn’t have the rights to read the private folder. So we kept looking.
| |
We could have set the GET parameter error to /var/www/private/config.ini, but unfortunately the error template was never printed. Still, this was odd. After some trial and error, we found this blog post. It shows a bug that uses a Perl-specific problem almost identical to the one here. It is basically an HTTP Parameter Pollution attack, as $query->param('error') can return a scalar or an array, depending on the context. We can use this to overwrite the header template file and get the flag that way. (Check the blog post for more details.)
https://school.fluxfingers.net:1501/?error=a&error=header&error=/var/www/private/config.ini
| |
Overall this challenge was really fun to solve. Thanks, lama, for such an awesome challenge.
Update 1
For some users the server time and their own time did not match, so on the server the key was generated in the future. By default, this means that GPG does not encrypt a message and stops instead. The site now uses --ignore-valid-from, so this should hopefully not happen anymore. If the output is still empty after uploading a valid public key, please let us know in the IRC channel.
Hint 1
You do not have to break crypto to solve this task. It also does not include any low-level exploitation.
Hint 2
The first step to solve this challenge is to get the source code of the site. You will need it to solve the second part, i.e., the bug is in the script.